Safeguarding against malicious downloads
If you are like me, a day probably doesn’t go by when you aren’t using the internet on your computer. Most likely you will be downloading a file from a website, whether this is a PDF, DOCX, ZIP or even an EXE file, but how do you know if these files are safe and secure or malicious downloads? Do you put all your trust in the website? Are they a well-known company? Do they say they run security checks frequently? These are the questions you need to ask yourself.
This article is going to talk about how to safeguard your computer and your information from malicious downloads, for the purpose of this article, it’s primarily going to be focussed on the Windows Operating System, but the majority of these actions can be carried over to other Operating Systems.
Think First
The first protection against protecting your computer and information is asking yourself, do I need this download, if you can have a look at the link that you are going to click on, is it executable (ending with .EXE, .BAT. SH, .MSI), if it is you may not want to download it unless you are of course downloading an application of sorts.
Antivirus
This is one of the questions I get asked all the time, in fact, I was asked this yesterday, is antivirus still relevant? Do I still need to run it? The simple answer is yes, it’s still relevant, although this can go by many names such as endpoint protection, antivirus/antimalware. It’s all still relevant and these products will protect you against not only the well-known viruses but ransomware and in most cases threats that come via email, such as phishing.
The next question no doubt in your mind is, which product should I get? There’s no simple answer to this, most of the time it’s down to personal taste, however, I’d lean more towards a major brand and pay a few pounds than utilising a free one. Personally, I’d recommend the products from ESET as I’ve never had an issue with these products in over the 15 years or so that I’ve used them. Although not a sales pitch, if you’d be interested in a trial or purchasing an ESET license, visit TeraByte’s website and ask about their offers.
Don’t use local administrator/root
The way we use Operating Systems is starting to change for the better, but we are still in a place where when you set up a new computer, your first user account has defaulted to a high privileged “system” account which allows you to do everything on your computer. This can be a dangerous situation to be in if you execute a malicious downloads application, or your computer is infected with malware.
You should not run your computer as an administrator/root level account for your day-to-day activities, you should only use this account when you need to execute or perform some high privileged activity, this will help you protect your computer from infection. This can be performed by creating a second account that has normal level access and using this one for your general day-to-day activities.
Creating a Linux user account
Creating a basic Linux user account is quite easy, first open a terminal window, then perform following the commands:
- sudo useradd <name>
- sudo passwd <name>
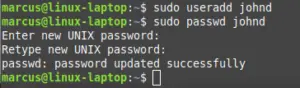
Once you have created the user, you can then decide whether you need to add the user to specific groups, but this is outside of the scope of this article today.
Creating a Windows user account
Creating a Windows user account is a little more in-depth, but is still simple to follow, there is an article here which shows you how to create a new account on Windows 10: https://www.laptopmag.com/articles/limited-user-accounts-windows-10
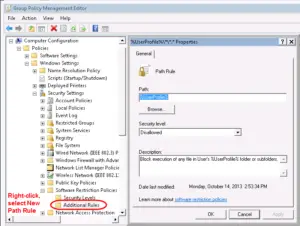
Block executables from running on download
When downloading files from the internet, they are usually saved in a “Downloads” directory, this can lend itself to unwanted execution of applications, or malicious downloads, especially within a more corporate environment. It is recommended that you should configure your account so that it takes two clicks (or actions) or more to open the specific file. Now, this may sound like an irritant, but do you way up a few seconds more compared to your business or information being ransomed? That’s a decision for you to decide upon.
For Windows, one of the best ways of protecting your Downloads folder from accidental execution is using Software Restriction Policies. With these policies, you can define what can or can’t be done and can be pushed out by using group policy for corporate environments, or configured locally on your home machine, if needed.
For our article, you can use Software Restriction Policies (SRP) to block any execution of files from the Downloads folder, thereby making the user copy/move the file of choice from its initial location to somewhere else, such as the Desktop, then allowing you to open the file. This process makes it so that you think about what you are doing and implements the two-action rule.
Remove unnecessary applications
Application bloat is a common thing, especially if you’ve been using your computer for any length of time, perform periodic checks on the applications you have installed, do you need them all? Have they all been updated to the most recent version? Where possible ensure that you configure automatic updates on all applications, to ensure that they are kept current.
Summary
I hope that this article helps you with safeguarding your computer and information, we’ve only scratched the surface of what you can do to protect your interests, however, if you would like to know more or get in touch, please visit our site at https://isgovern.com for more information and to view the services that we offer.
